Security the Basics
Lesson 7: Generic hashes
Generic hashes are one-way values that can be generated from a very short or very long amount of data. They are hard to manipulate and are mostly used to for things such as checking file integrity or indexing.
Coding a simple hash in DataFlex
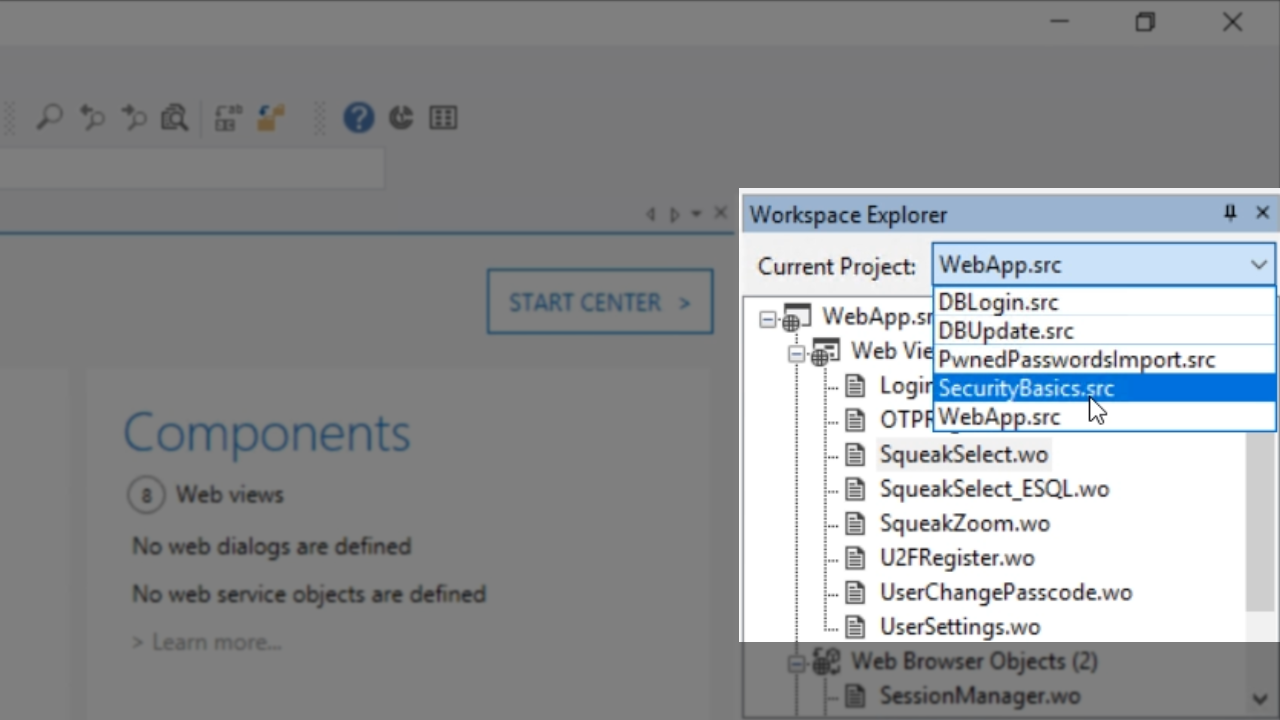
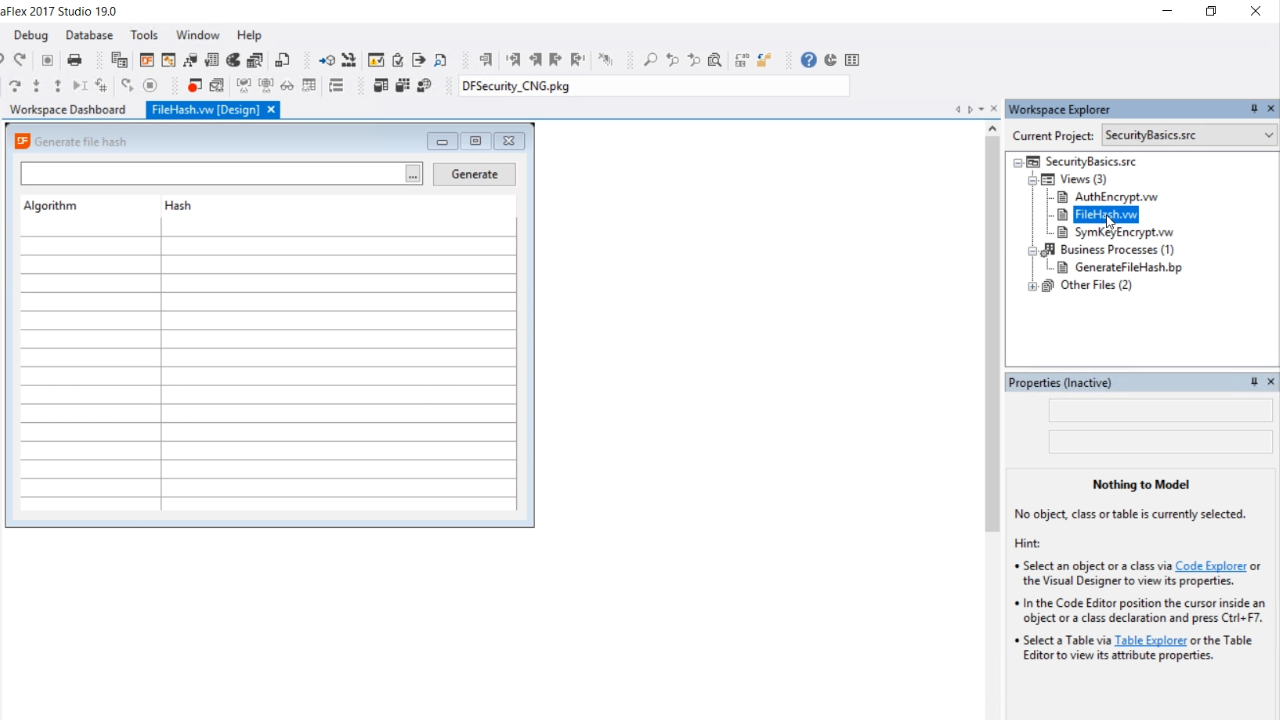
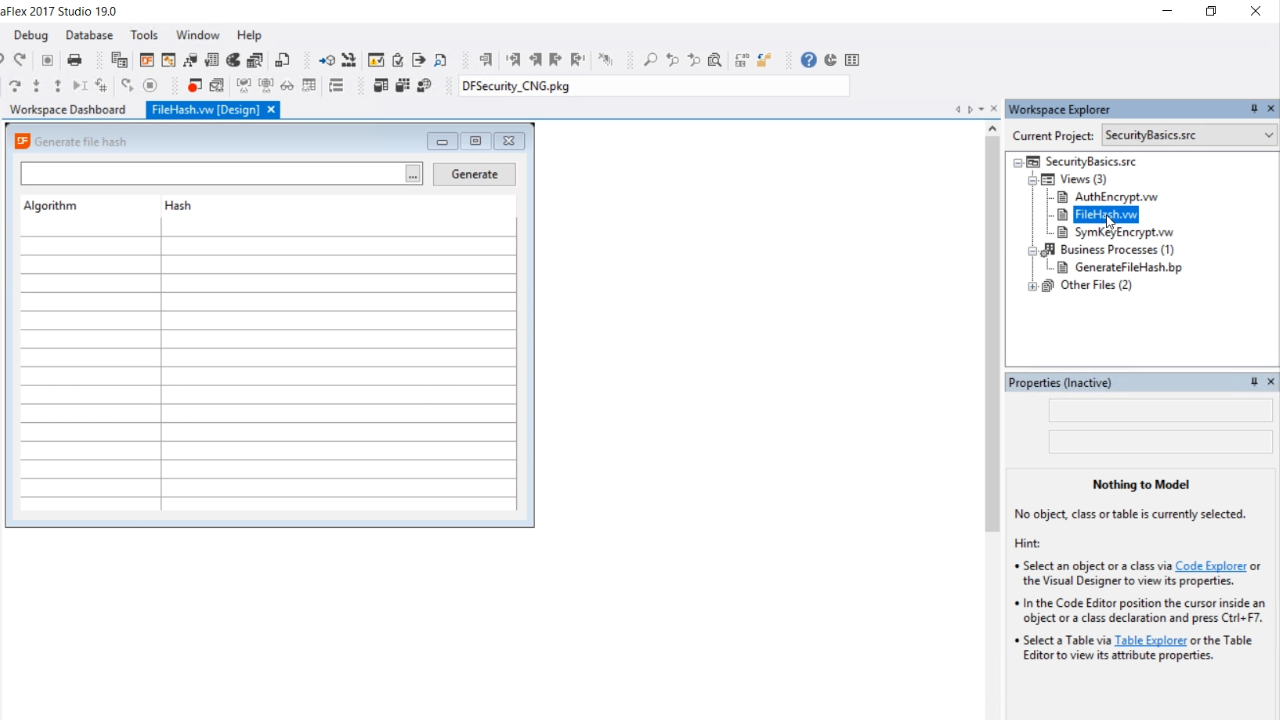
- For this example, a simple Windows project called SecurityBasics.src will be used.
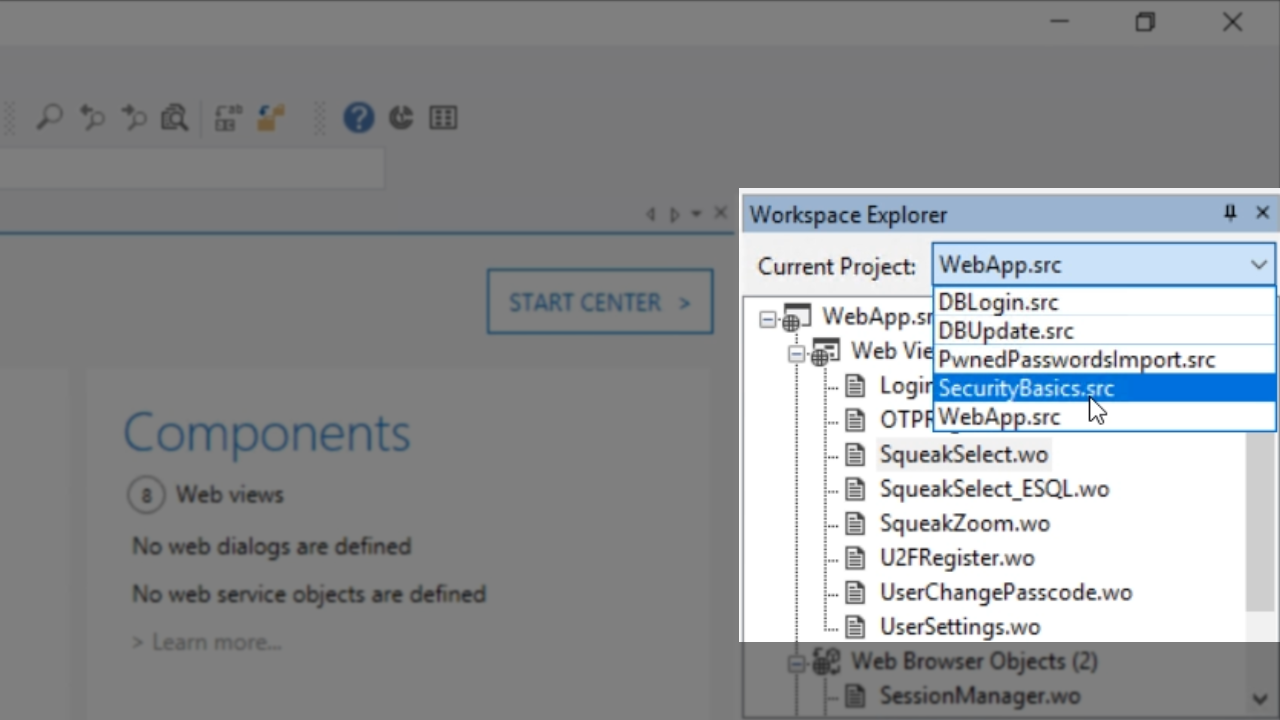
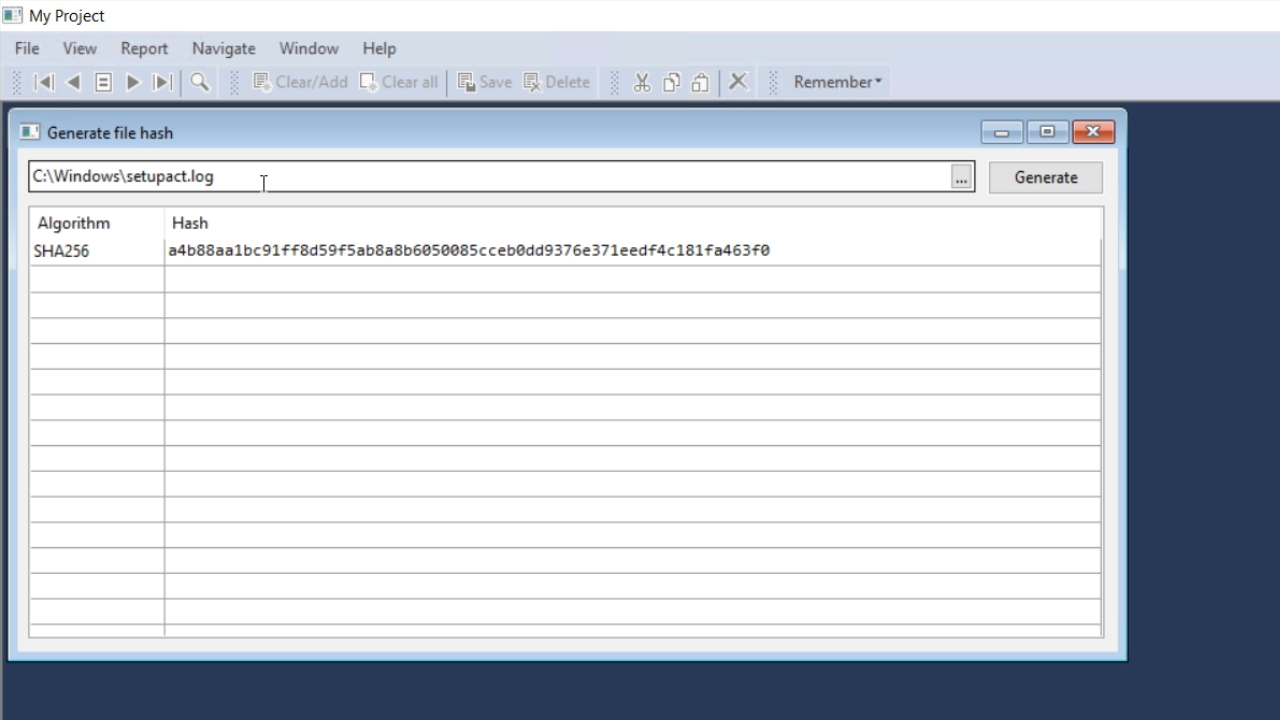
- From the ‘Workspace Explorer’ panel on the right, double click ‘FileHash.vw.’ This view allows a user to select a file, and then a hash is generated according to a specific algorithm.
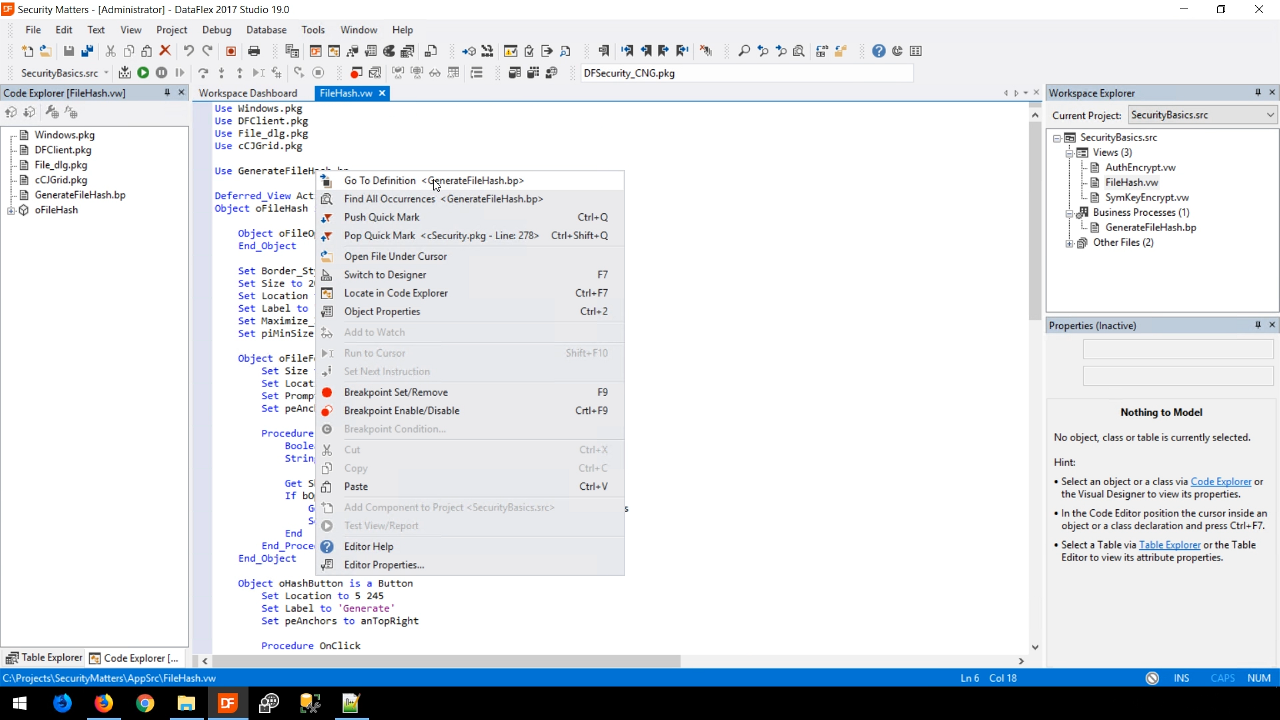
- From the code view of FileHash.vw, right click on GenerateFileHash.bp, and select ‘Go to definition.’
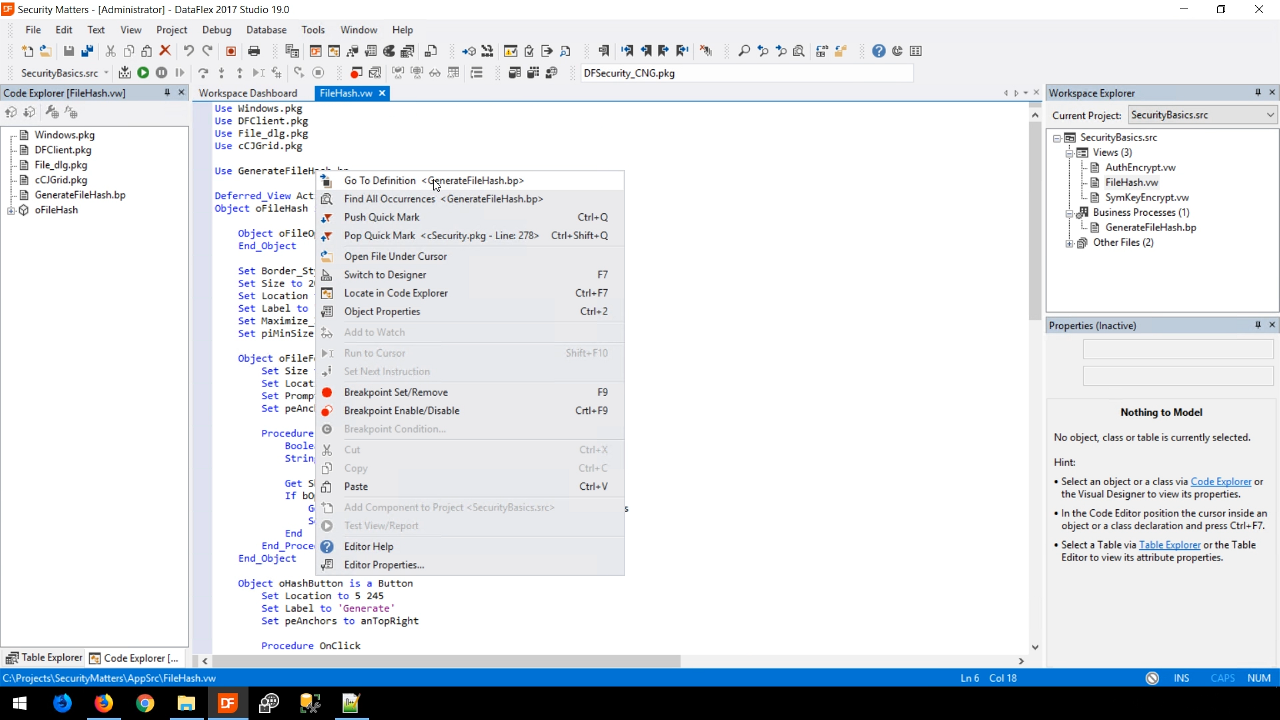
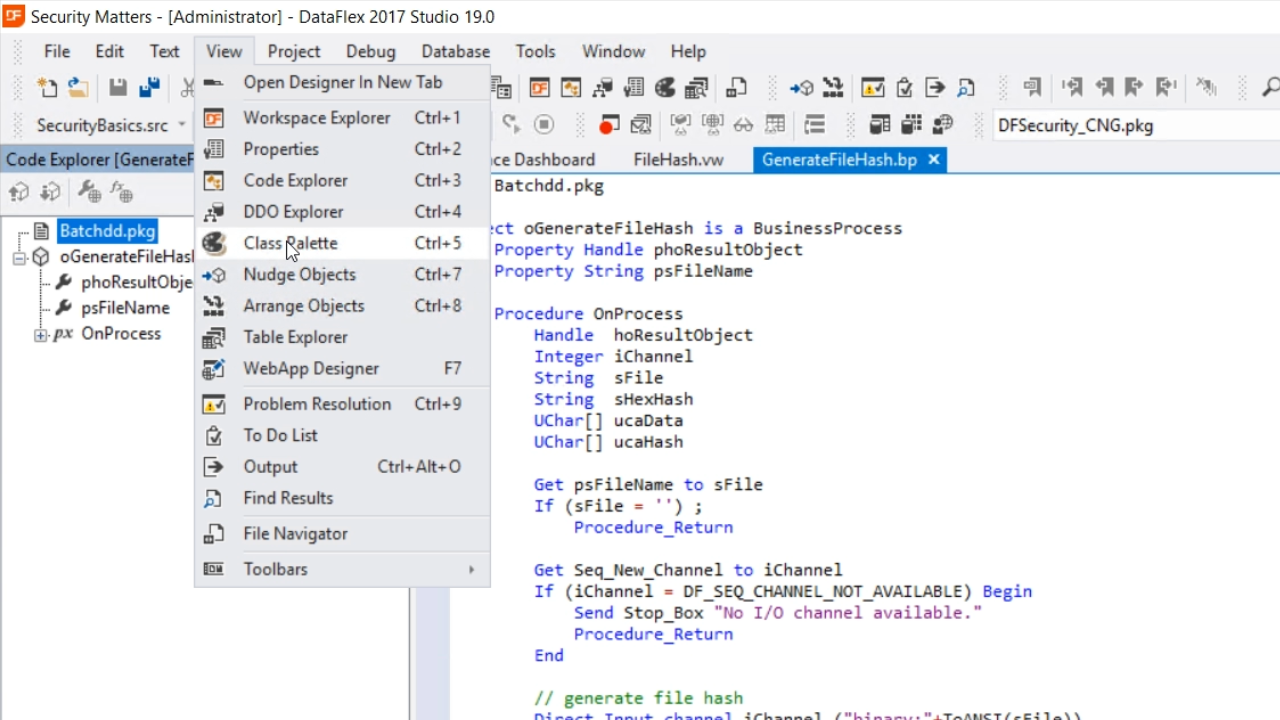
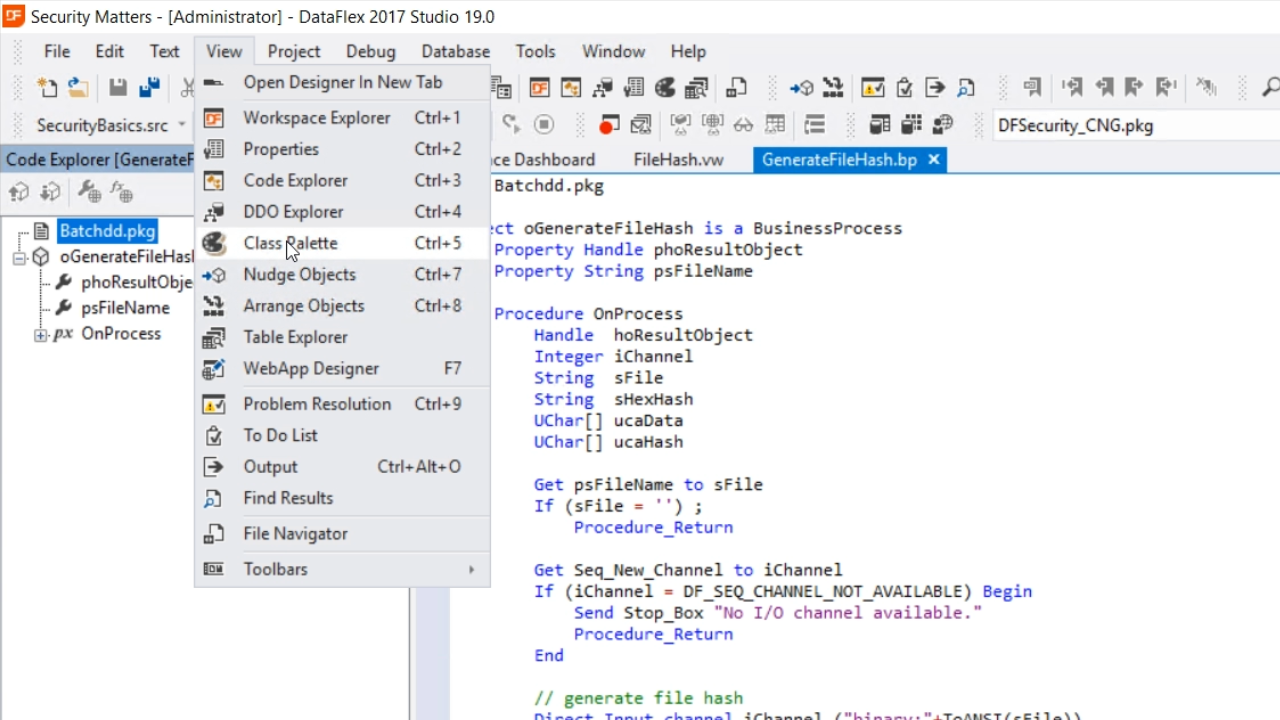
- This business process opens the file and reads it. Only a few ToDos need to be done to it. First, open the Class Palette panel by selecting VIEW from the top menu and selecting ‘Class Palette.’
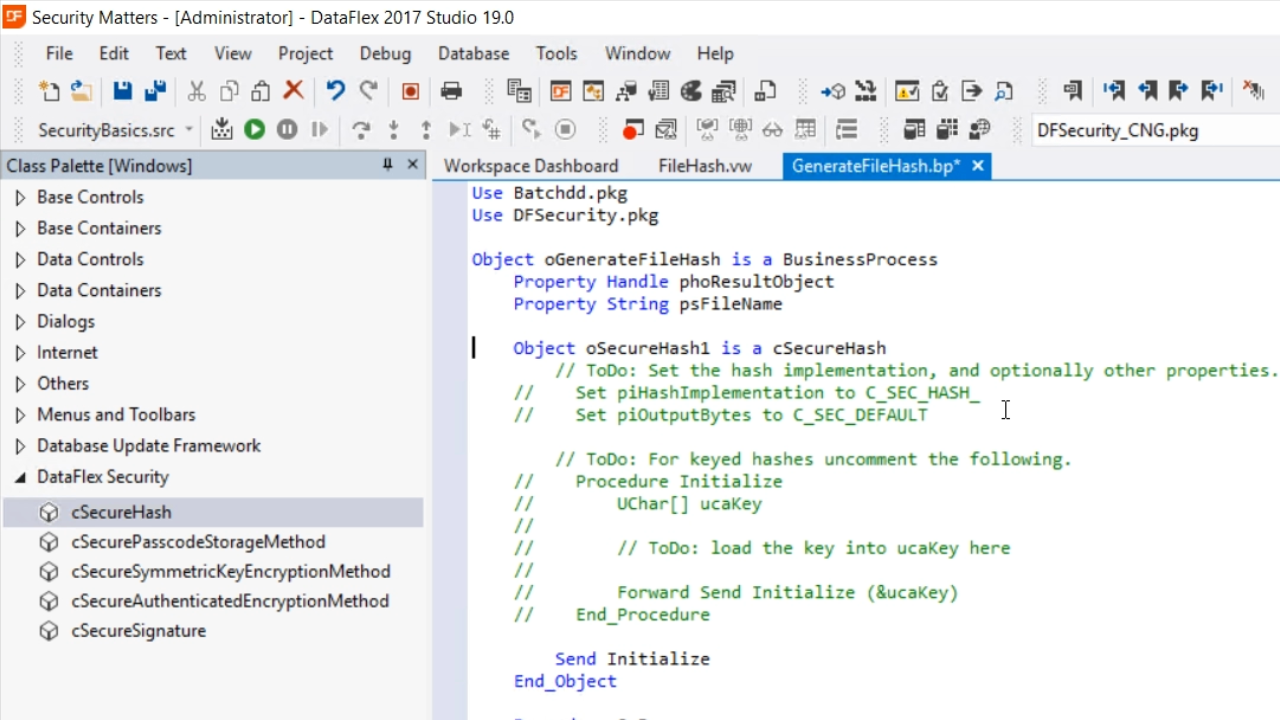
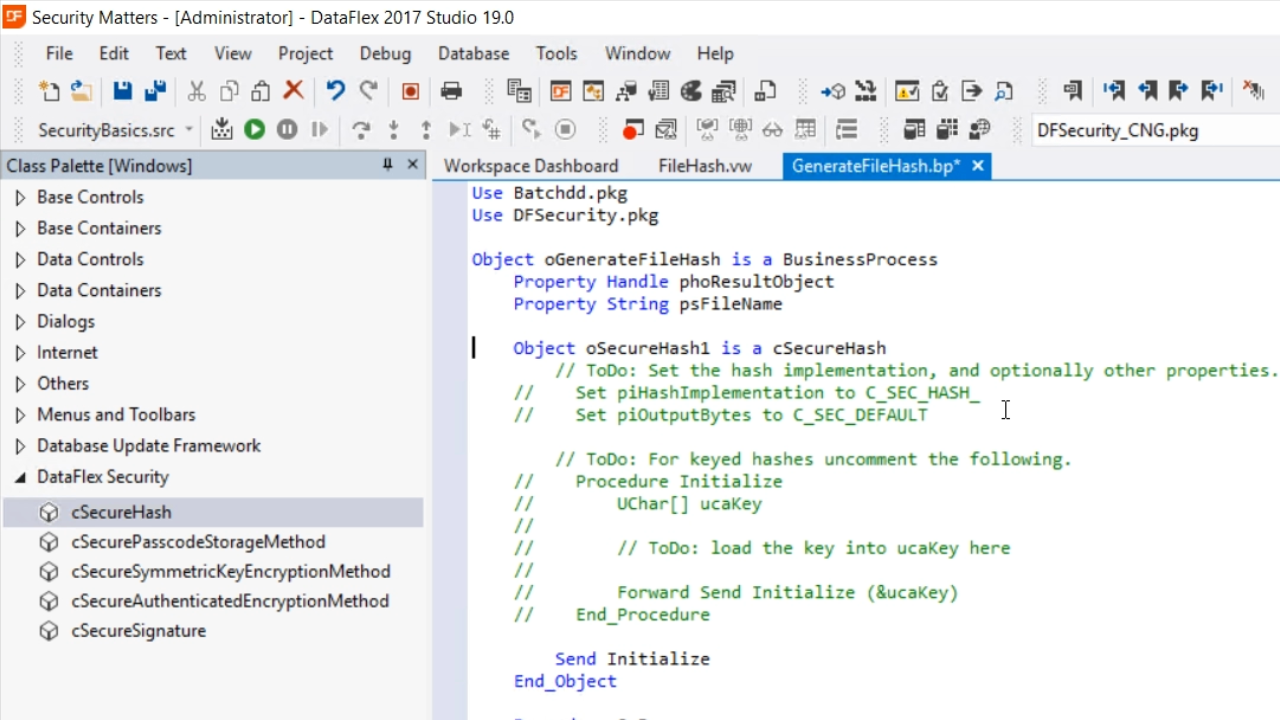
- Then, from the palette panel on the left, expand ‘DataFlex Security,’ and drag-and-drop ‘cSecureHash’ into the code.
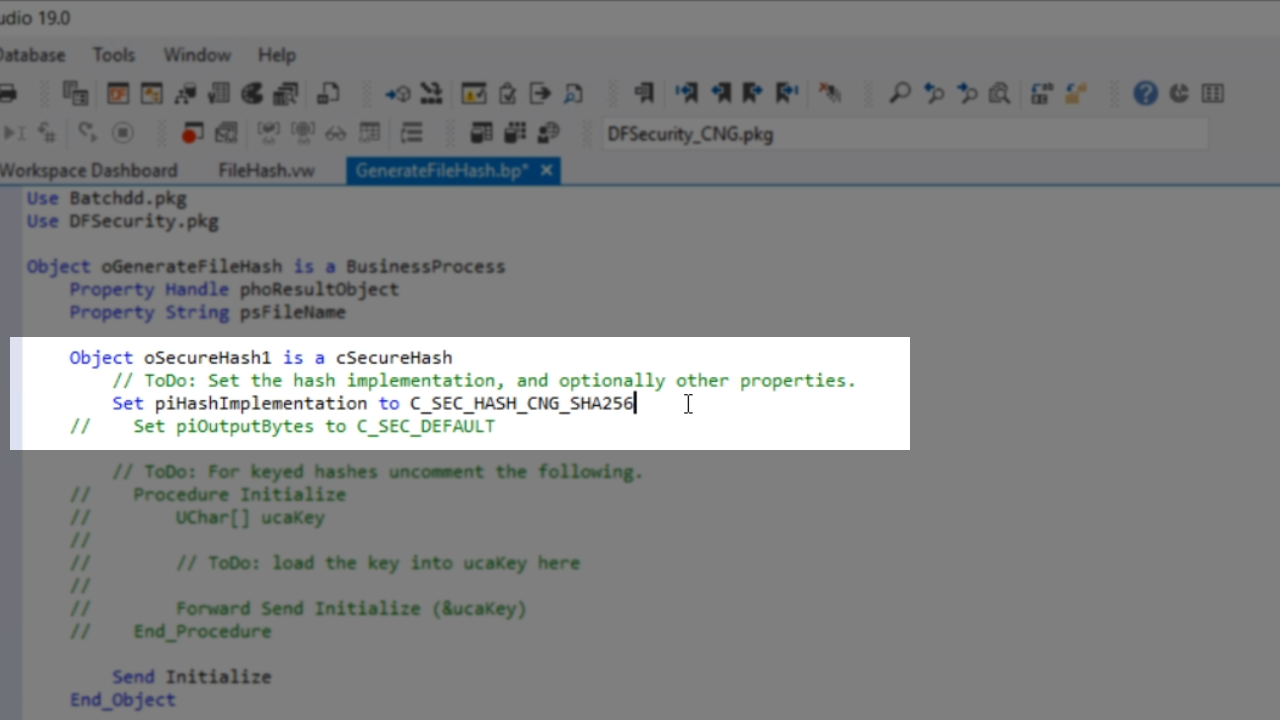
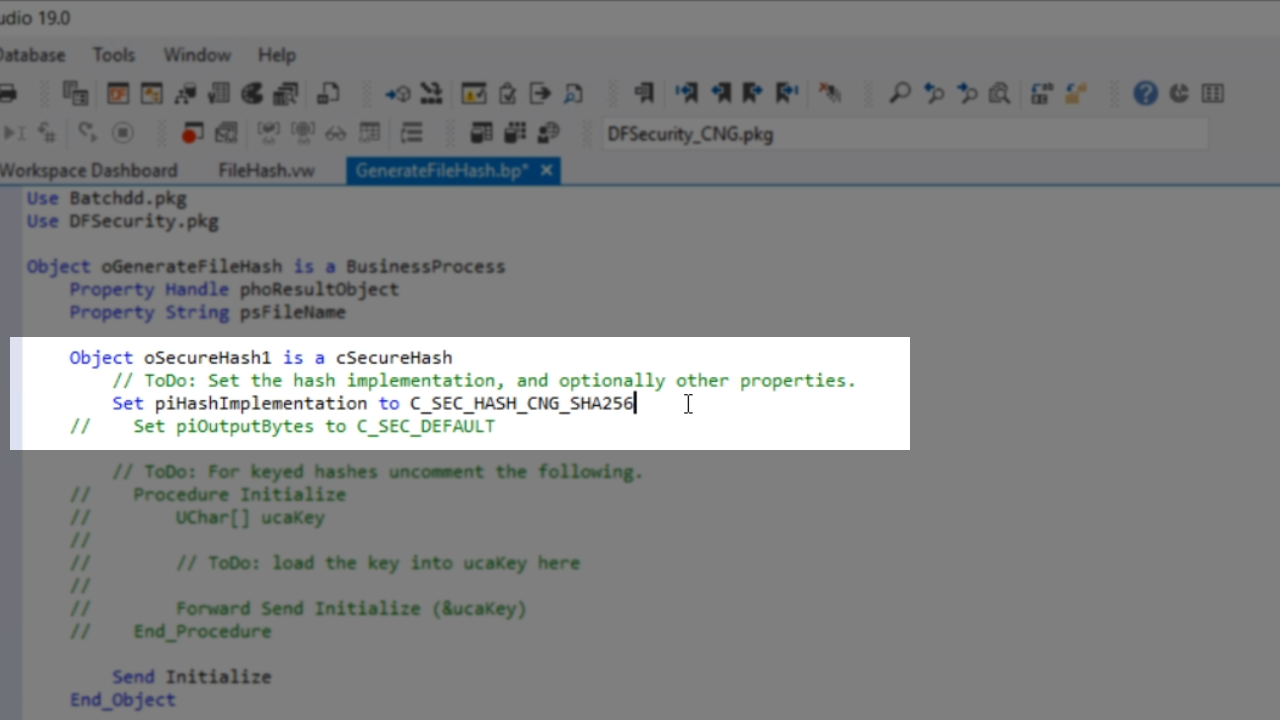
- The first ToDo in the template is to set piHashImplementation. A very simple one is used for this example, C_SEC_HASH_CNG_SHA256. This is standard in Windows, so it is the easiest. Copy the name of the object – cSecureHash1.
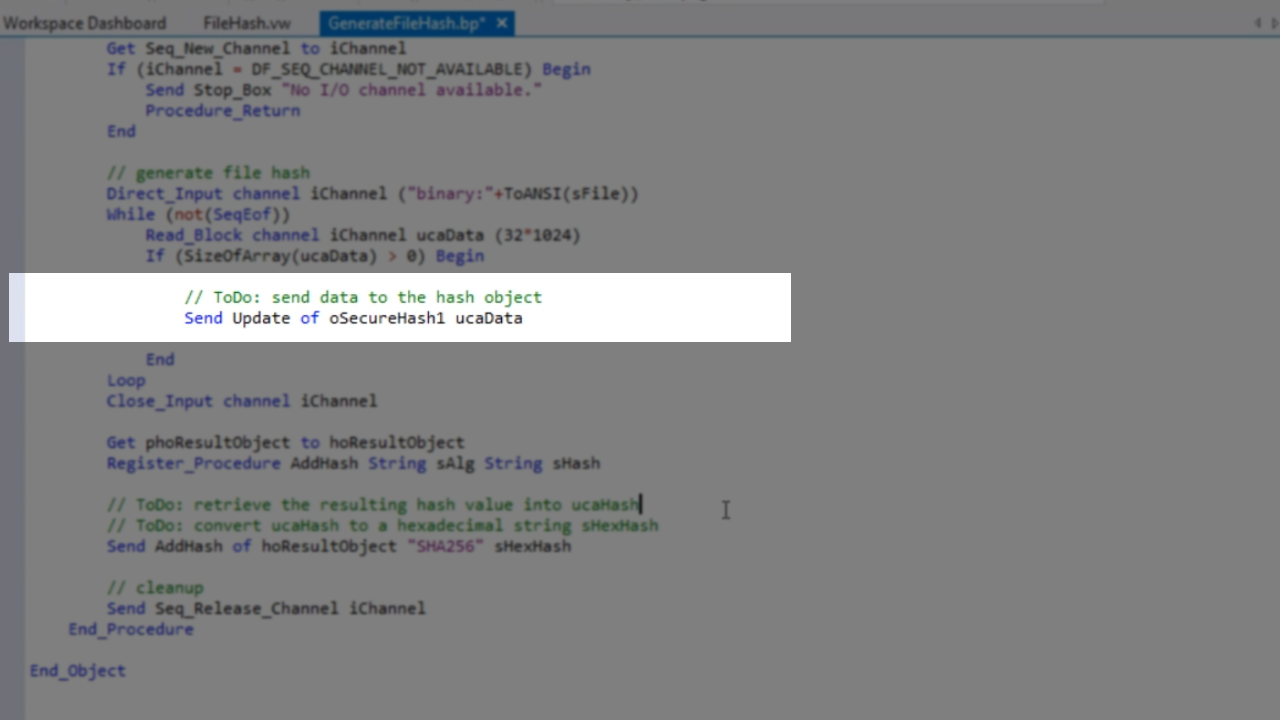
- Further down in the code, the data will need to be sent to the hash object. The hash object will process all the data sent to it and will then generate a fixed sized hash. To do so, the following is added to the code…
Send Update of oSecureHash1 ucaData
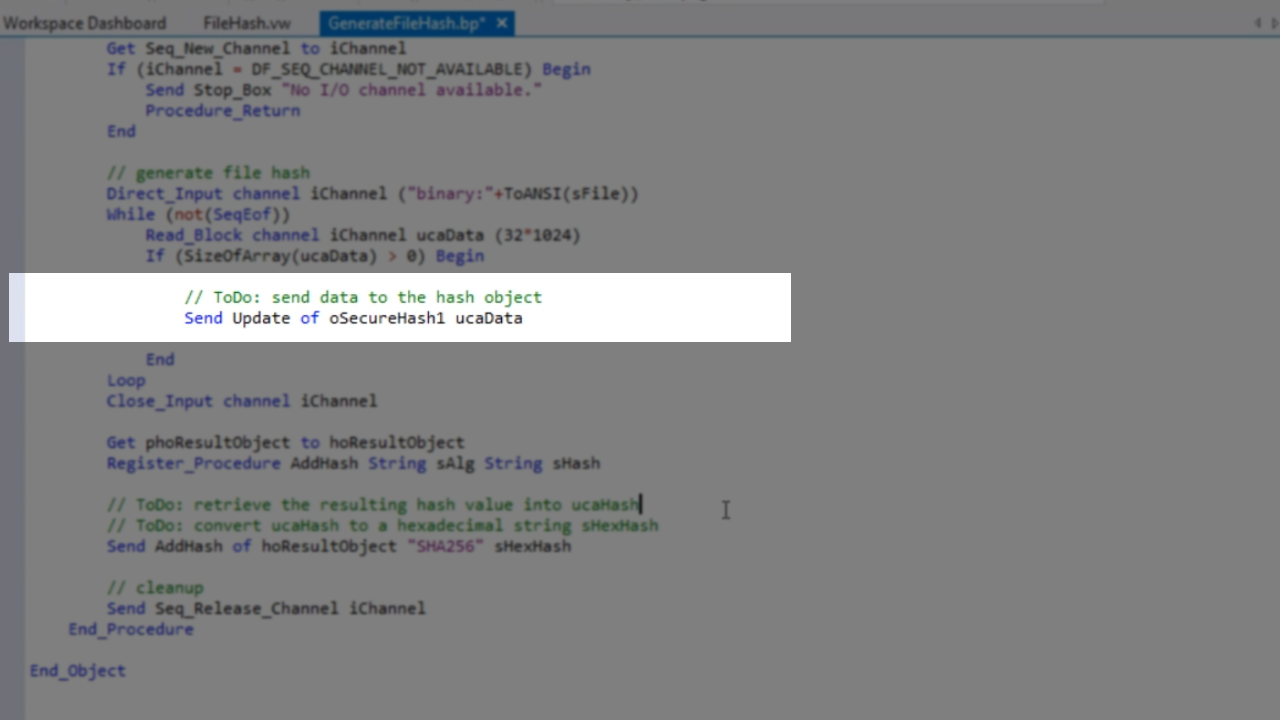
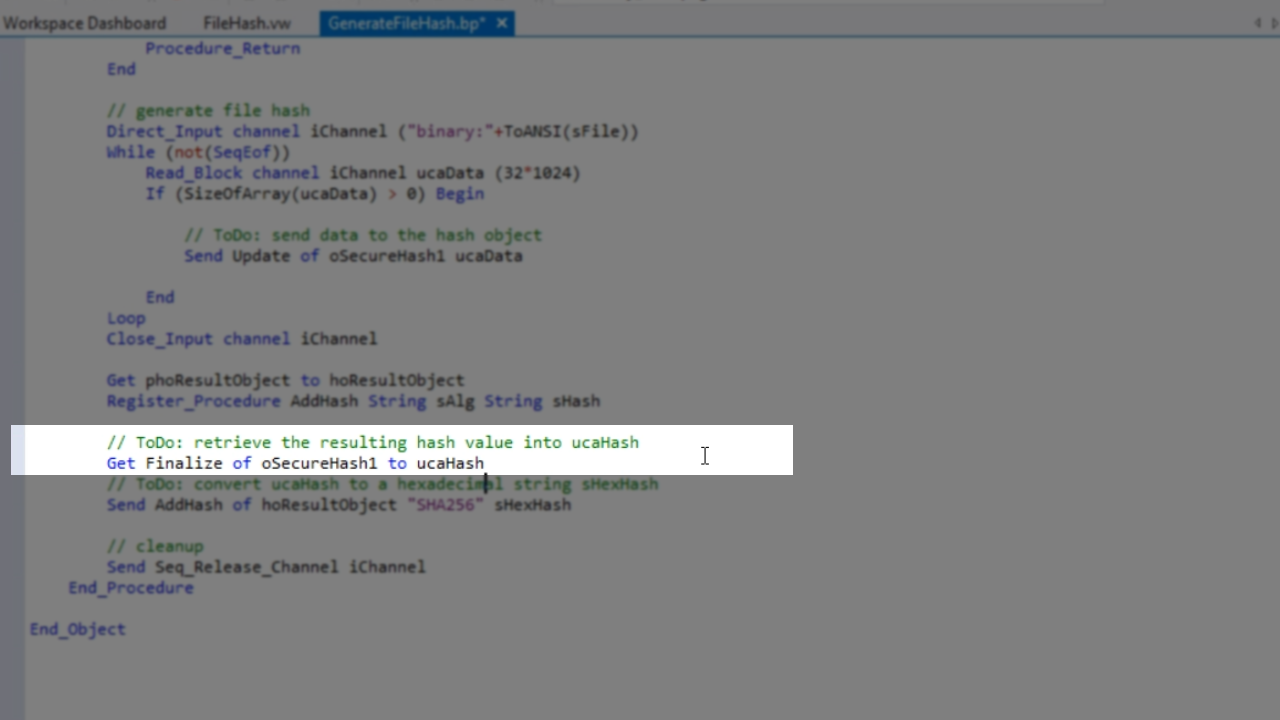
- Once all the data is received, the hash object needs to produce the hash value. To do so, the following is added to the code…
Get Finalize of oSecureHash1 to ucaHash
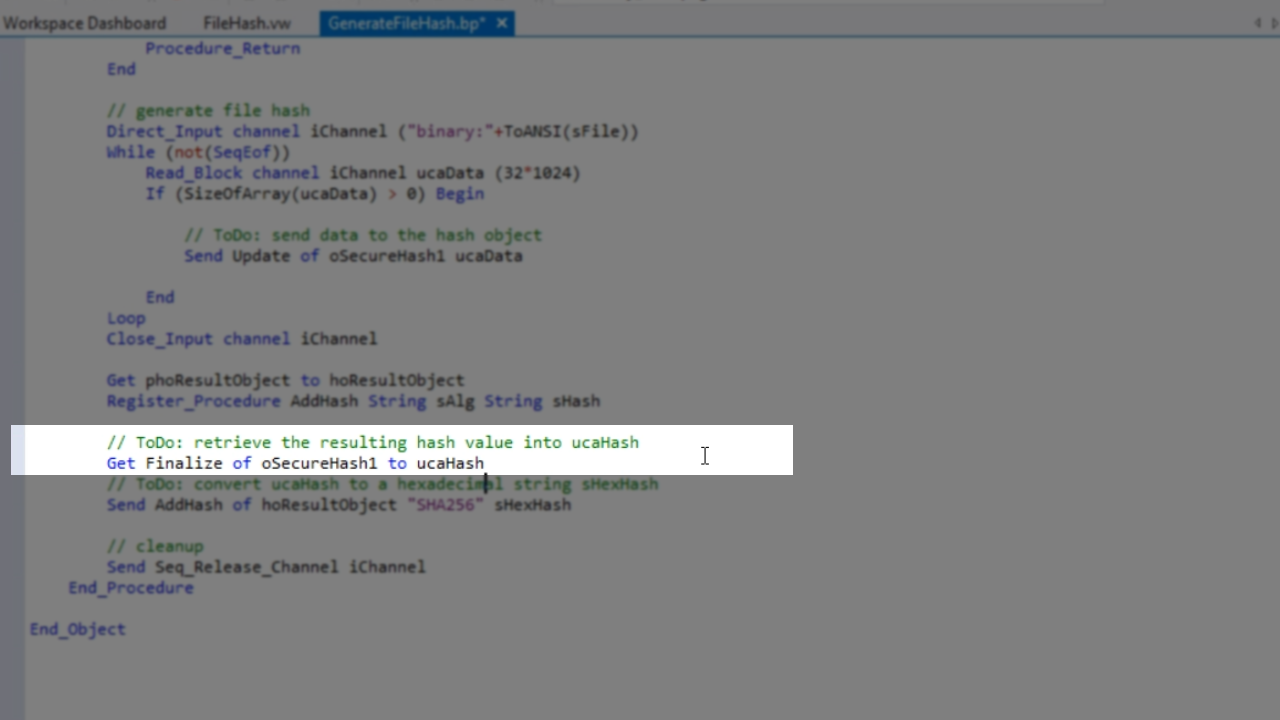
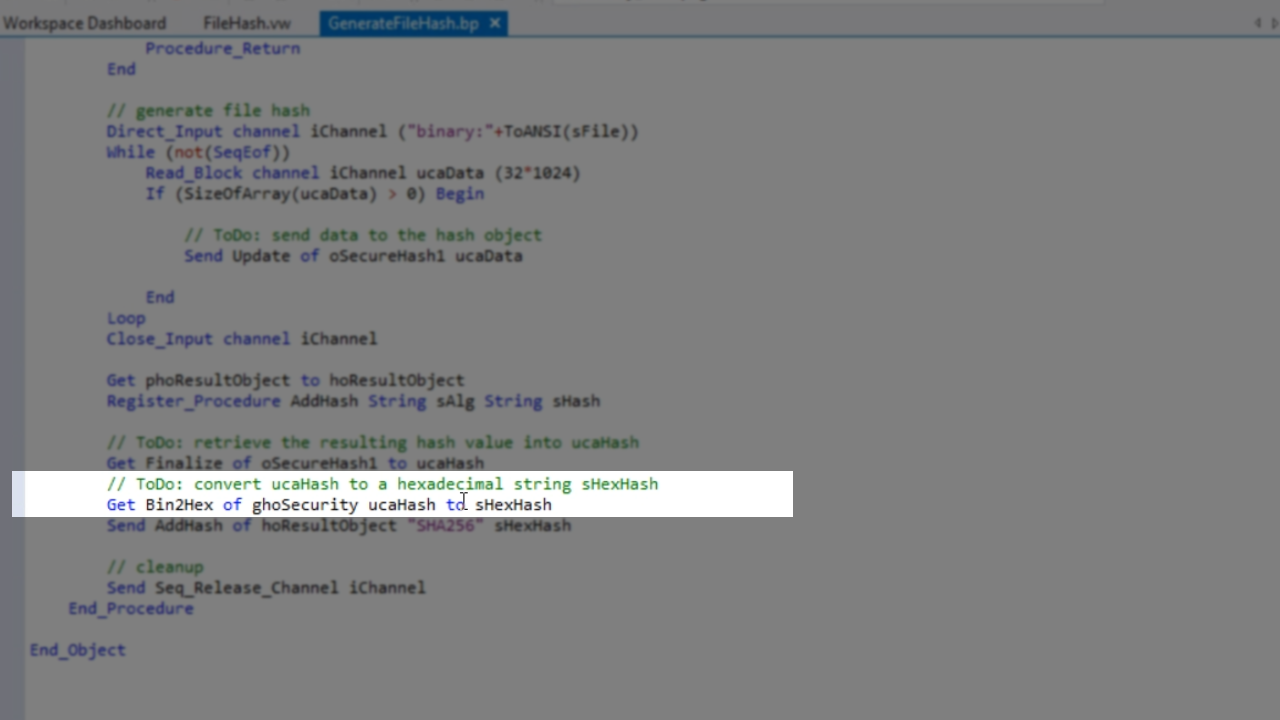
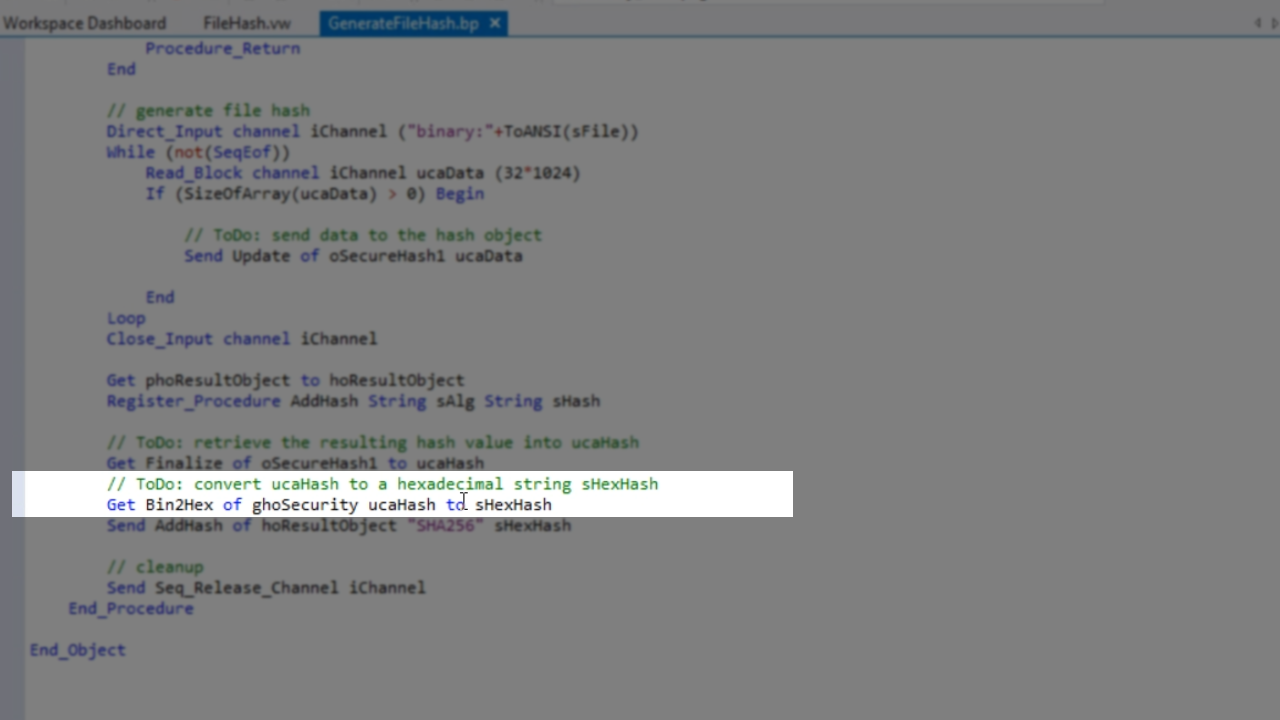
- The binary data needs to be converted. Hexidecimal is easiest for debugging, so that is what will be used here
Get Bin2Hex of ghoSecurity ucaHash to sHexHash.
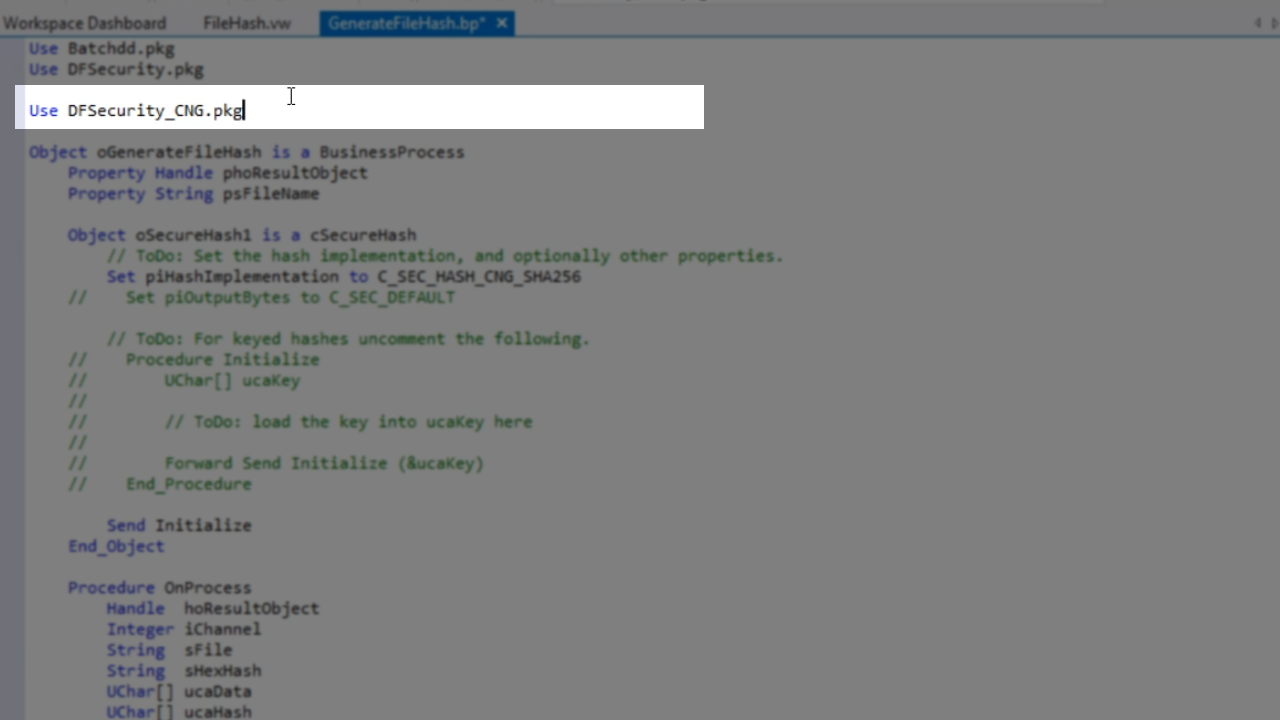
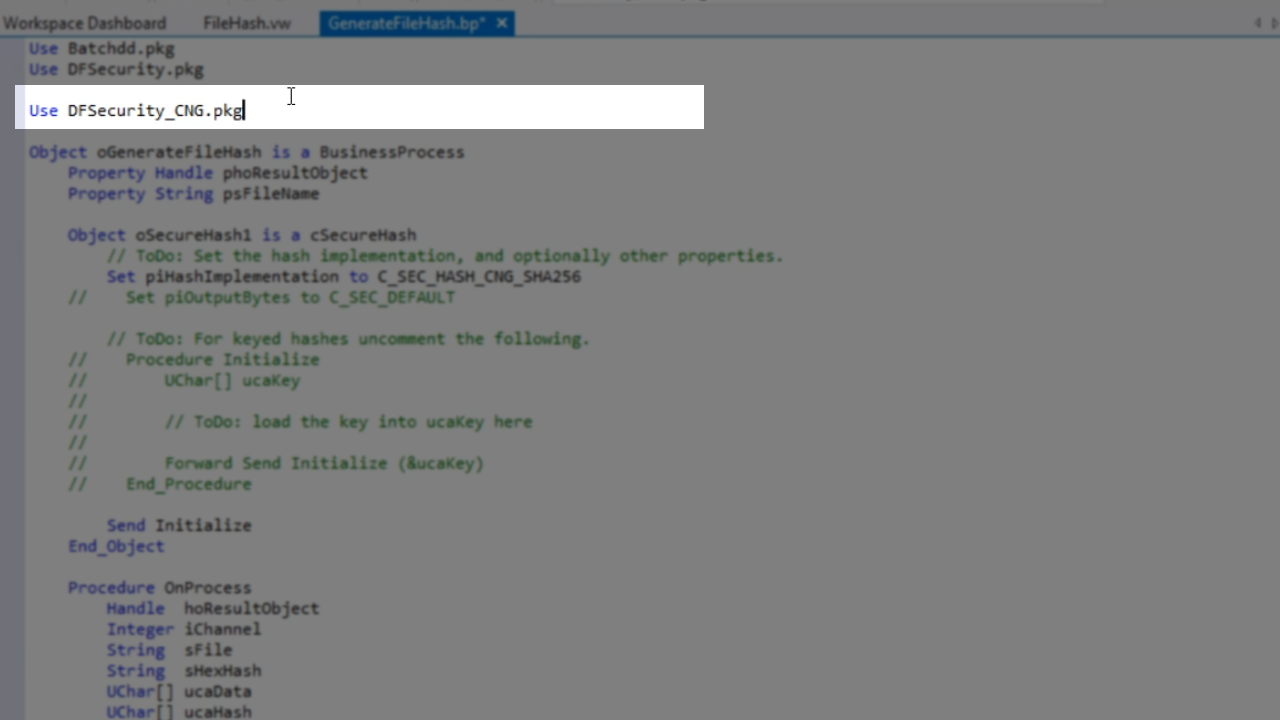
- An engine also needs to be included. On top of the code is added:
Use DfSecurity_CNG.pkg
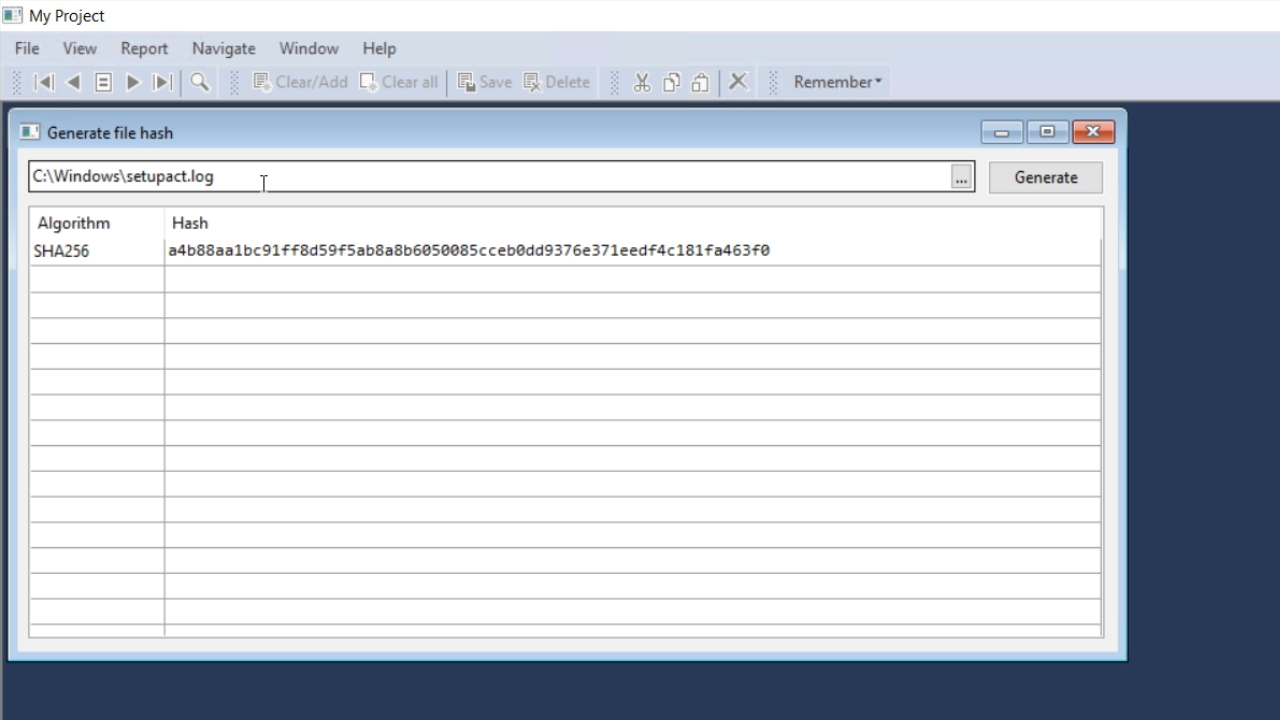
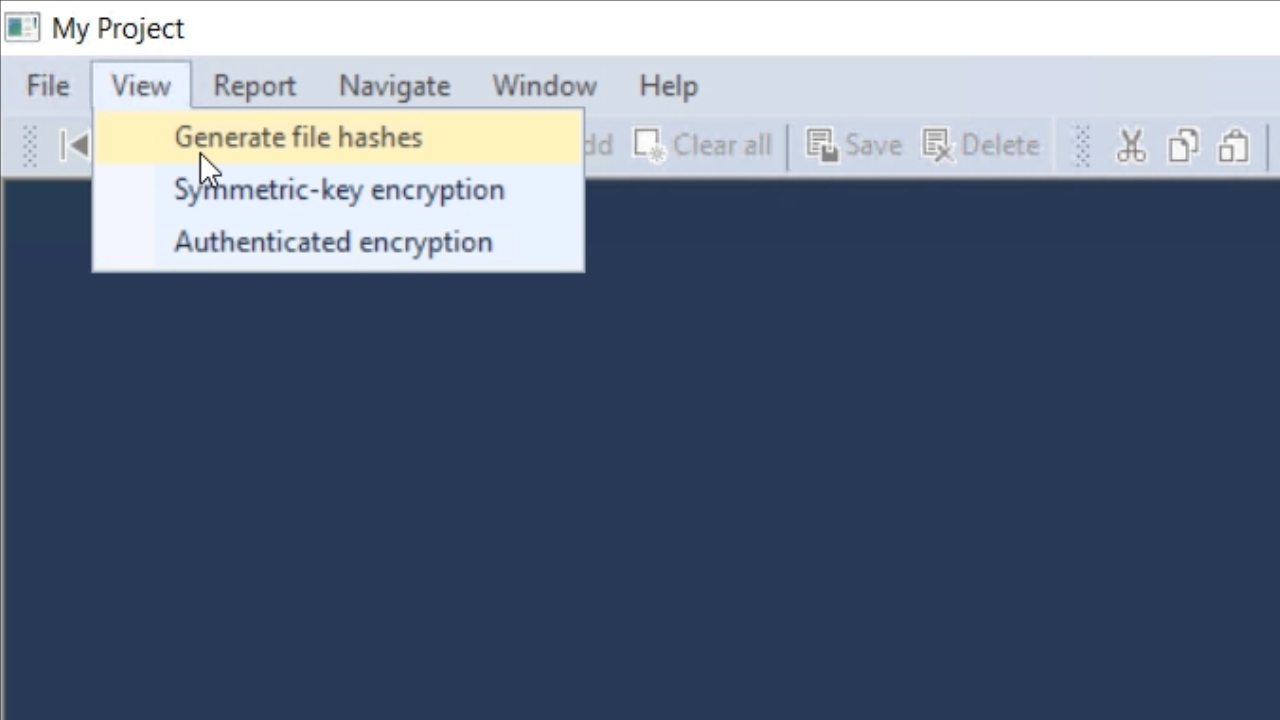
- Press F5 to run the code. From the application screen, select VIEW from the top menu and then GENERATE FILE HASHES.
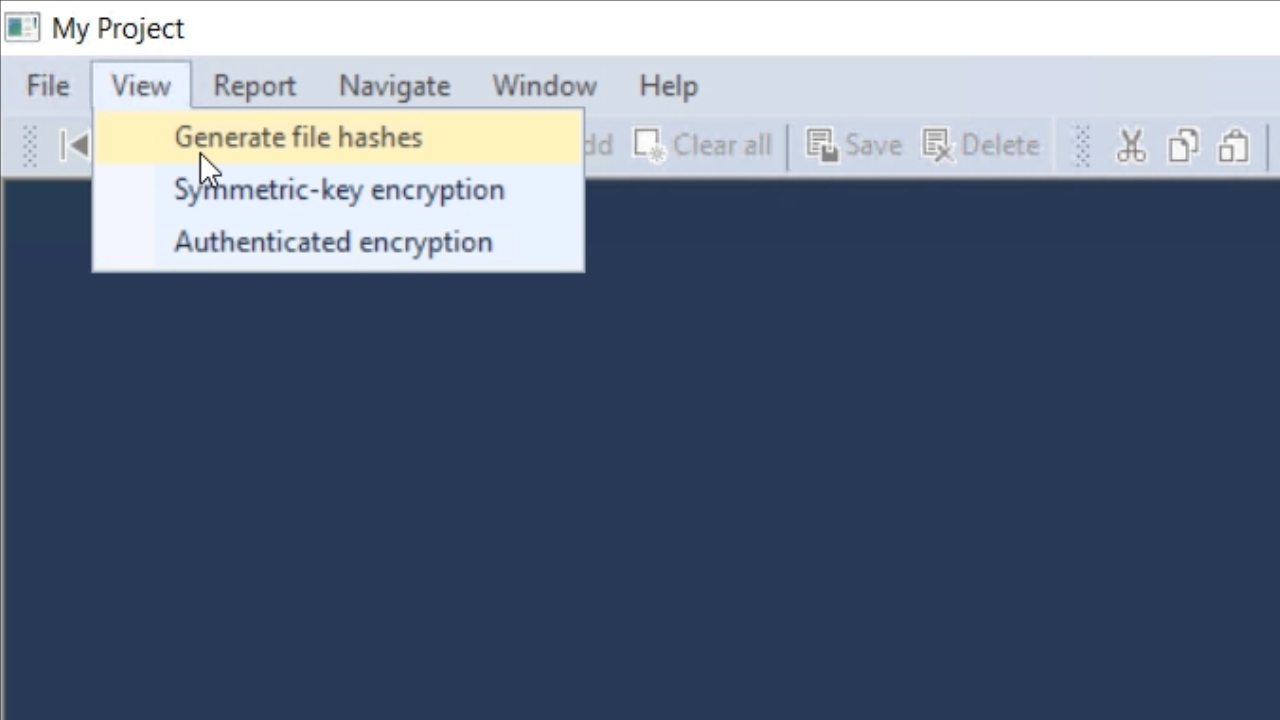
- Any file can be opened. Pressing the GENERATE button will result in a hexadecimal value for the file. The hash will not change if GENERATE is pushed multiple times.